The command center for cybersecurity operations.
Derive’s Operations Module turns plans into measurable action. Run workflows like user access reviews, incident response, and vendor risk assessments - all prioritized by quantified loss reduction.
Where cybersecurity execution meets measurable impact.
The Operations Module bridges the gap between strategy and execution. Every workflow feeds back into your Governance and Risk data - showing exactly how operational activities reduce loss.
Workflows that tie directly to risk.
From third-party to AI risk assessments, every task is linked to the controls and risks it affects.
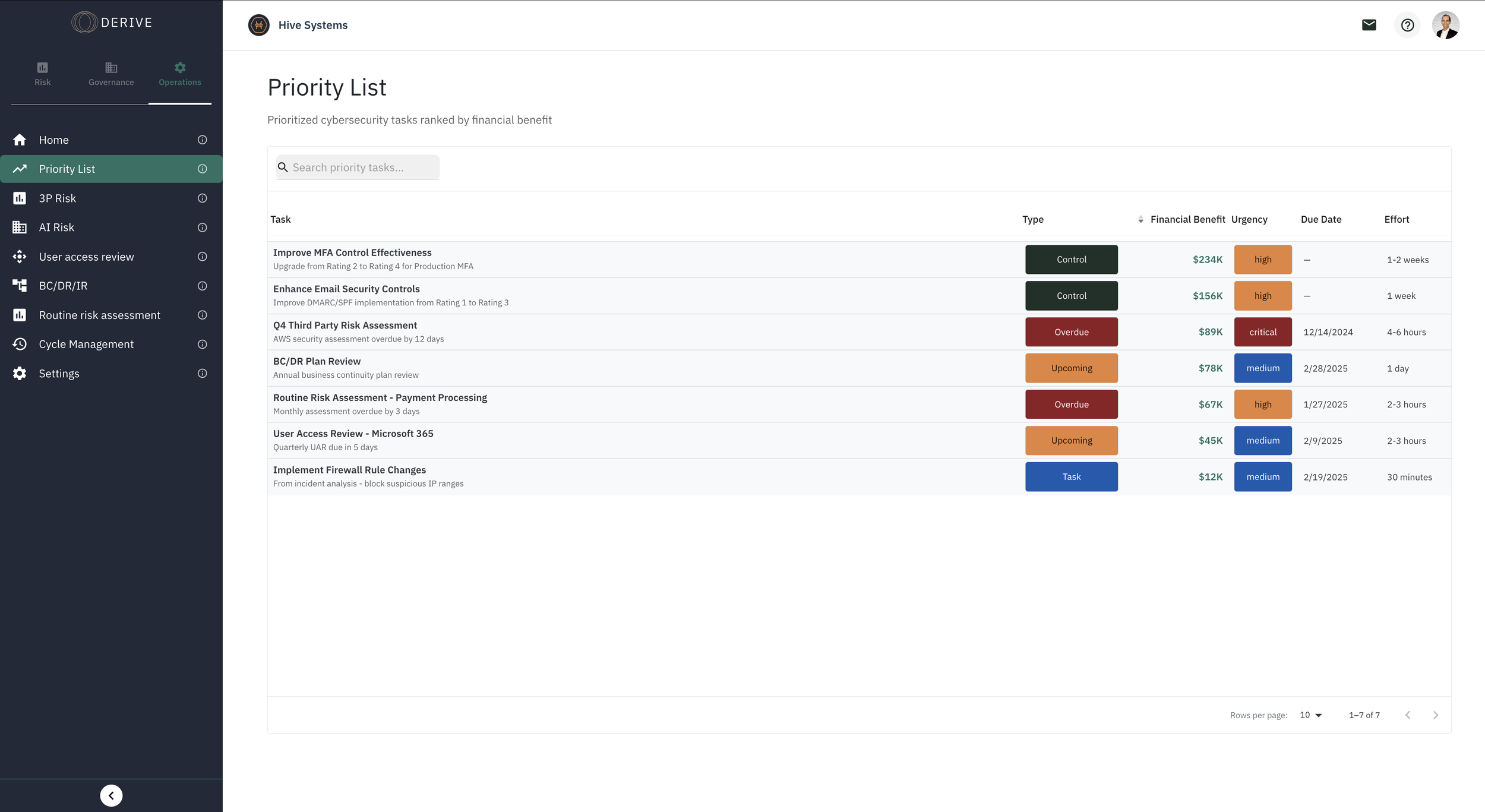
Always know what comes next.
The Priority List ranks cybersecurity actions by financial benefit, effort, and urgency - so teams focus where impact is highest.
Stay organized with the Operations Calendar.
Every workflow and review is automatically added to your Operations Calendar, giving you a clear view of cybersecurity activity across time.
Frequently Asked Questions
Have other questions? →Reach out any time
-
The Operations Module turns quantified cyber risk into prioritized daily action.
It provides built-in workflows for real cybersecurity tasks such as user access reviews, third-party risk management, AI risk assessments, incident response, and BC/DR planning. Every task is ranked by measurable financial impact, ensuring cybersecurity operations are directly tied to risk reduction.
-
The Operations Module generates a real-time priority list ranked by expected loss reduction per dollar spent.
Instead of completing tasks based on habit, audit cycles, or leadership pressure, teams execute workflows based on modeled financial impact. This creates true cyber risk prioritization driven by data, not guesswork.
-
Every workflow inside the Operations Module updates the Risk Module automatically.
As tasks are completed, controls mature, deadlines are missed, or exceptions are logged, expected monetary loss recalculates in real time. This creates continuous cyber risk monitoring and shows how operational execution directly affects financial exposure.
-
Yes.
The Operations Module replaces spreadsheets, disconnected ticketing systems, and fragmented tracking tools with structured, built-in workflows. These workflows are directly connected to governance and risk modeling, ensuring operational activity drives measurable cybersecurity investment ROI.
-
Because operational tasks are tied to financial risk modeling, leaders can see exactly how completed work reduces exposure.
Executives and boards receive clear, measurable updates showing which actions reduced risk, where exposure remains, and how cybersecurity operations are improving financial resilience. This transforms operational reporting into board-ready cybersecurity reporting grounded in real dollars.

Ready to connect cybersecurity actions to measurable impact?
Ask about Derive’s Operations Module, built-in workflows, or how to tie activities directly to loss reduction.
Our team has the answers.